Aegis transit security enforcement
Aegis delivers transit security enforcement in live traffic paths so teams can adopt stronger cryptographic profiles incrementally without blind cutovers.
Ingress
Service-to-service
Egress
mTLS
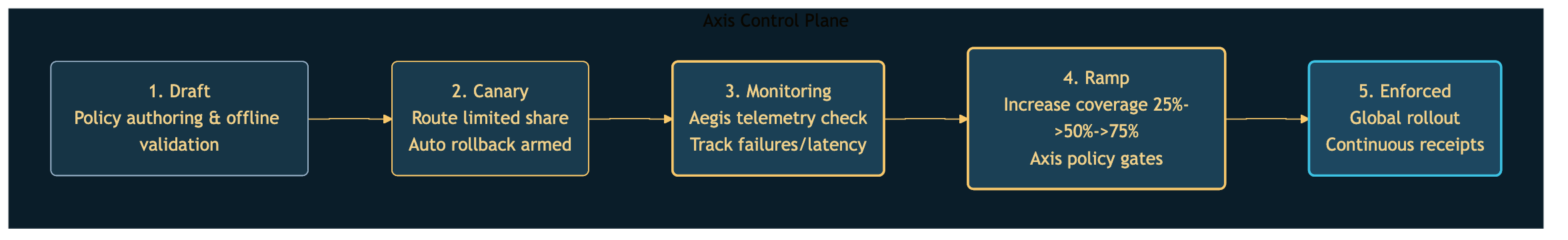
Rollout safety
Built for controlled policy adoption under operational constraints.
- Policy-based negotiation strategy
- Safe fallback and rollback controls
- Posture and compatibility telemetry
- Evidence generation for audits
Who this is for
Teams that need in-line enforcement
- Platform teams that run gateways or service mesh boundaries.
- Security teams that need one policy model across ingress, east-west, and egress traffic.
- Programs that require staged rollout evidence before expanding scope.
Transit security enforcement in practice
↔ Swipe to pan diagram
Enforces policy in transit
Aegis applies cryptographic controls in front of workloads so policy decisions are enforced where connections are established.
Supports staged adoption
Teams can scope by environment and traffic segment, then expand after compatibility and latency checks.
Publishes operator evidence
Aegis reports negotiation outcomes to Axis so rollout decisions and results are reviewable later.
Trust boundary with Axis
Aegis responsibilities
- Enforces transit policy in traffic paths.
- Collects compatibility and posture telemetry.
- Does not own tenant policy approval workflow.
Axis responsibilities
- Defines policy lifecycle and rollout checkpoints.
- Stores rollout records and audit receipts.
- Does not terminate workload traffic in place of Aegis.
Deployment constraints
- EC2 gateway model and Kubernetes DaemonSet model are both supported.
- Rollout order should be environment-segmented to contain blast radius.
- Control-plane connectivity and cert trust must be validated before enforcement mode changes.

